Meet Industry-Recognized Cybersecurity Standards
ISO 27001 Compliance, Assessment and Implementation
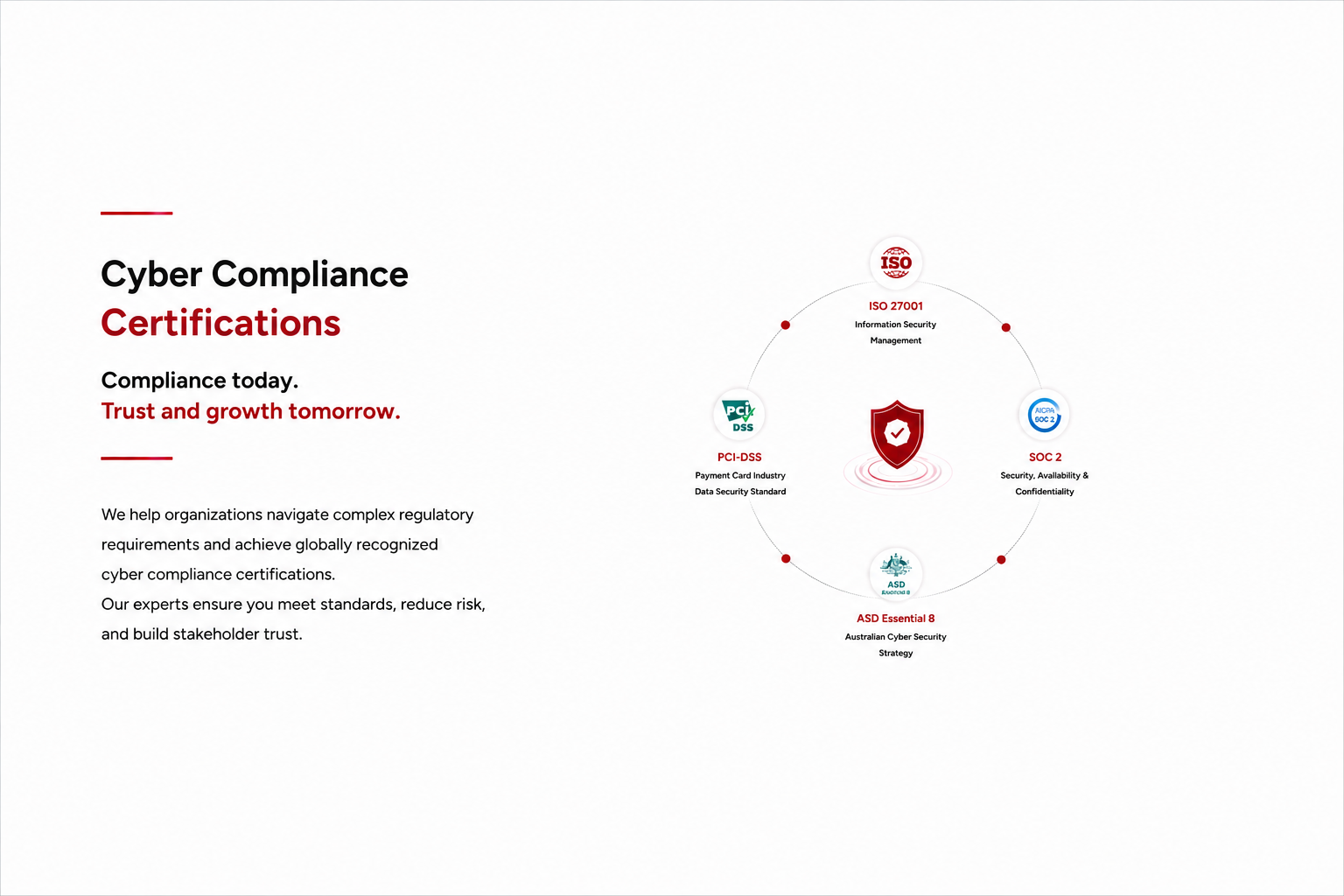
Align your organization with ISO 27001 standards in Australia with ATNIS. We provide end-to-end services—from gap analysis and ISMS implementation to audits and certification—ensuring expert-led, compliant, and efficient information security programs.

SOC 2 Audit Services
SOC 2 certification is essential for businesses in SaaS, fintech, and cloud services, where data security and privacy are critical. ATNIS helps organisations achieve SOC 2 compliance, strengthening security, demonstrating robust data management practices, and building trust with customers and stakeholders.

PCI-DSS Compliance
Safeguard customer credit card information and strengthen your organisation’s ability to process payments securely with PCI DSS compliance.ATNIS PCI DSS Compliance Services offers a range of services including PCI DSS-Discovery, Validation, Gap Analysis and PCI DSS Audit

ASD Essential 8 Cyber Security Services
Protect your organisation from cyber threats. Our expert team specialises in helping businesses achieve and maintain ASD Essential 8 compliance. We provide comprehensive solutions, including risk assessments, security strategy development, implementation, and ongoing monitoring.

Frequently Asked Questions
What is PCI DSS and why is it important for our business?
PCI DSS is a global security standard designed to protect cardholder data during processing, storage, and transmission. Compliance helps businesses reduce fraud, protect customer data, and maintain trust with payment partners such as Visa, Mastercard, American Express, and Discover Financial Services.
Is PCI DSS compliance mandatory?
Yes. Any organization that stores, processes, or transmits payment card data must comply with PCI DSS requirements. Non-compliance can lead to penalties from acquiring banks and card brands.
How long does ISO 27001 certification take?
Typical implementation timelines:
-
Small organisations: 3–6 months
-
Mid-size companies: 6–9 months
-
Large enterprises: 9–12+ months
What are the key components of ISO 27001?
Major elements include:
-
Risk assessment and risk treatment
-
Security policies and governance
-
Access control and identity management
-
Asset management
-
Incident response management
-
Business continuity planning
-
Continuous monitoring and auditing
How long is ISO 27001 certification valid?
Certification is valid for three years, with annual surveillance audits to ensure continued compliance.
What is the Essential 8 Framework, and how does it help businesses mitigate cybersecurity risks?
The Essential 8 is a framework developed by the Australian Signals Directorate (ASD) to provide businesses with key cybersecurity strategies. These strategies, such as patch management, multi-factor authentication (MFA), and restricting administrative privileges, aim to reduce the risk of data breaches and ensure operational continuity by proactively mitigating vulnerabilities.
How do Essential 8 maturity levels impact cybersecurity compliance?
The framework includes four maturity levels, with Level 0 indicating minimal security practices and Level 3 representing advanced, proactive cybersecurity measures. Achieving higher maturity levels helps organisations align with government standards and ensures they are prepared to counter emerging threats effectively, reducing the likelihood of cyber incidents disrupting business operations.
What should organisations look for in an ASD Essential 8 Service Provider?
When selecting an ASD Essential 8 service provider, organisations should consider the following:
- Expertise and Certifications: Look for a provider with a proven track record and relevant certifications.
- Comprehensive Services: The provider should offer a range of services, including risk assessments, security audits, vulnerability scanning, and incident response.
- Proactive Monitoring and Maintenance: Continuous monitoring of systems and networks is essential for early threat detection and rapid response.
- Compliance Expertise: The provider should have a deep understanding of the Essential 8 framework and can help organisations achieve and maintain compliance.
- Strong Customer Support: A responsive and knowledgeable support team is crucial for addressing security issues promptly.
- Security Best Practices: The provider should adhere to industry best practices and stay up to date with the latest security trends.

Tell us how we
can help you
ATNIS does not share or disclose your information to third parties.Serving customers by looking forward as well as back is a big promise, but the power of today’s new digital capabilities is vast and growing.